Why Bluetooth Low Energy Is Safe for Mobile Identity Apps
Bluetooth® low energy (BLE) is deployed in billions of mobile devices around the world, which means it is subject to strict scrutiny and regular security checks and updates. However, despite this track record and the lack of threat in the Bluetooth protocols, Bluetooth Low Energy is still viewed, in some quarters, as a security risk in mobile identity applications. But Bluetooth Low Energy should be used with confidence. Here’s why:
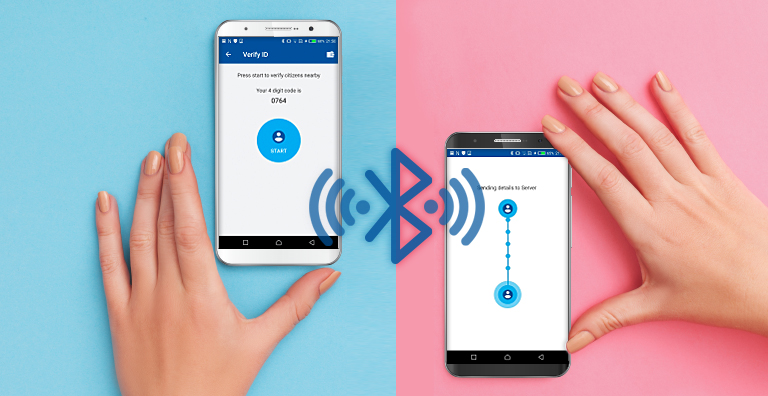
Bluetooth Low Energy Enhances the User Experience
Bluetooth Low Energy is critical to an effective mobile ID because it maximizes the reach and contributes to an enhanced user experience. Bluetooth Low Energy allows data transfer at a larger distance than NFC, which has two benefits:
- It is safer for law enforcement officers approaching a potential suspect
- It quickens the passage of individuals through gates, doors or checkouts by engaging as the person approaches rather than waiting until the person is within a few centimeters of the verification device
Security Protocols Secure the Use of Bluetooth Low Energy
The emerging standards for mobile identity, ISO18013-5 for mobile driving license and ISO23220 for mobile eID, look closely at the security of Bluetooth Low Energy and specify engagement protocols that ensure the security of data transmission through an exchange of keys between the holder’s device and the verification device to create an encrypted channel. By sharing data through this channel, attacks such as man in the middle, eavesdropping and data injection are prevented. This approach also allows detection of attacks resulting in the mobile app and the verification device terminating the communications and thus protecting the data.
A Good Implementation Is Key to Bluetooth Low Energy's Success
So, with all of those protections in place, what’s the problem? While the standards have mitigated many of the technical threats, there can still be attacks if Bluetooth Low Energy is poorly implemented. A sophisticated attack with automation could exploit poor implementation workflows. This type of attack can insert malicious code which intercepts sensitive communications. These types of attacks are not mitigated by the standards. However, these attack vectors are preventable through best practice implementation of Bluetooth Low Energy in both the mobile identity app and the verifying devices.
Bluetooth Low Energy Can Be Used Confidentially in Mobile Identity Applications
In conclusion, while threats to Bluetooth Low Energy do exist, the standards go a long way towards mitigating the risks presented to data when a verification of a mobile ID takes place. Other attacks are possible through legacy hardware or faulty implementation, but employing best practice in design, security policy and app delivery significantly reduces any risk of compromise. Bluetooth Low Energy should therefore be used with confidence in mobile identity apps and verifying devices to realize enhanced user experience and encourage adoption. It is only by delivering the convenience of new technology that new mobile identities will be successful.
If you are thinking of implementing a mobile identity solution such as HID’s goID™ in your country, read more about why Bluetooth Low Energy is the go-to technology for mobile identity applications for governments and citizens in our white paper Why Bluetooth Low Energy (BLE) is Secure for Mobile ID Verification.
Steve Warne is Senior Director, Product Marketing, Citizen Identification Solutions, where he is responsible for the marketing and solution strategy related to the development and growth of HID’s government ID business. Steve has more than 15 years of experience in the government identity market